Our Services
We Are Providing Digital Services
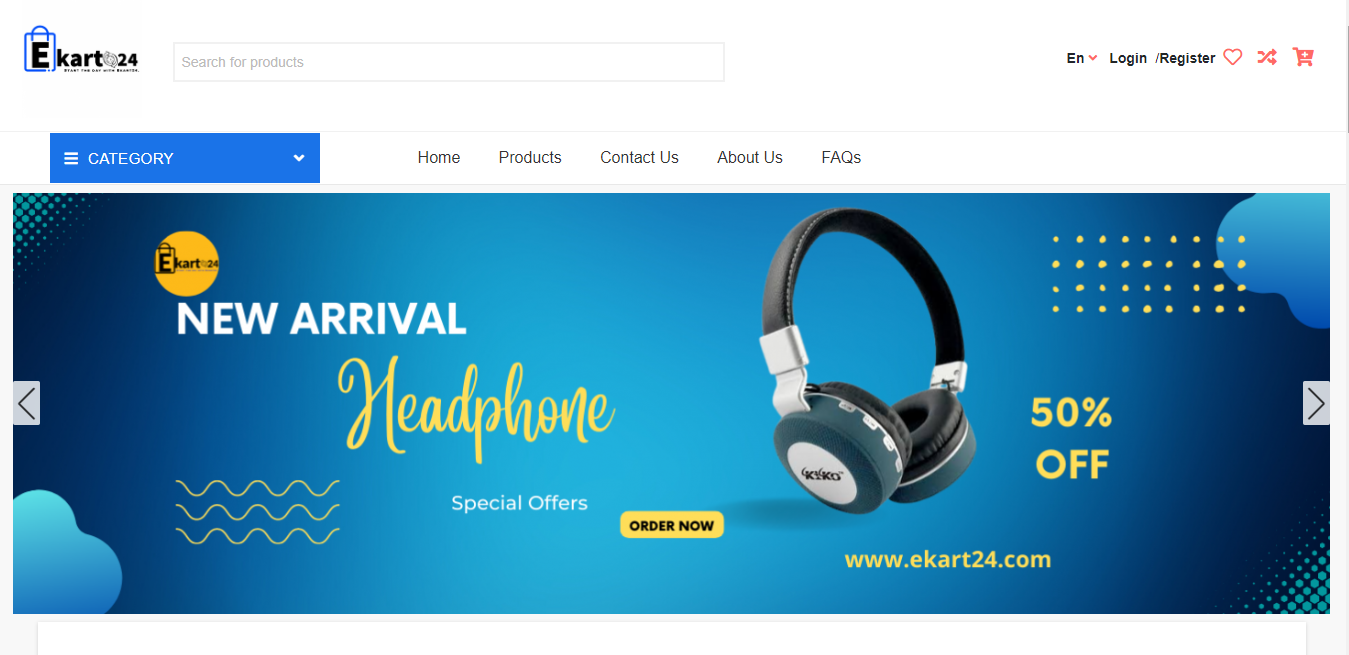
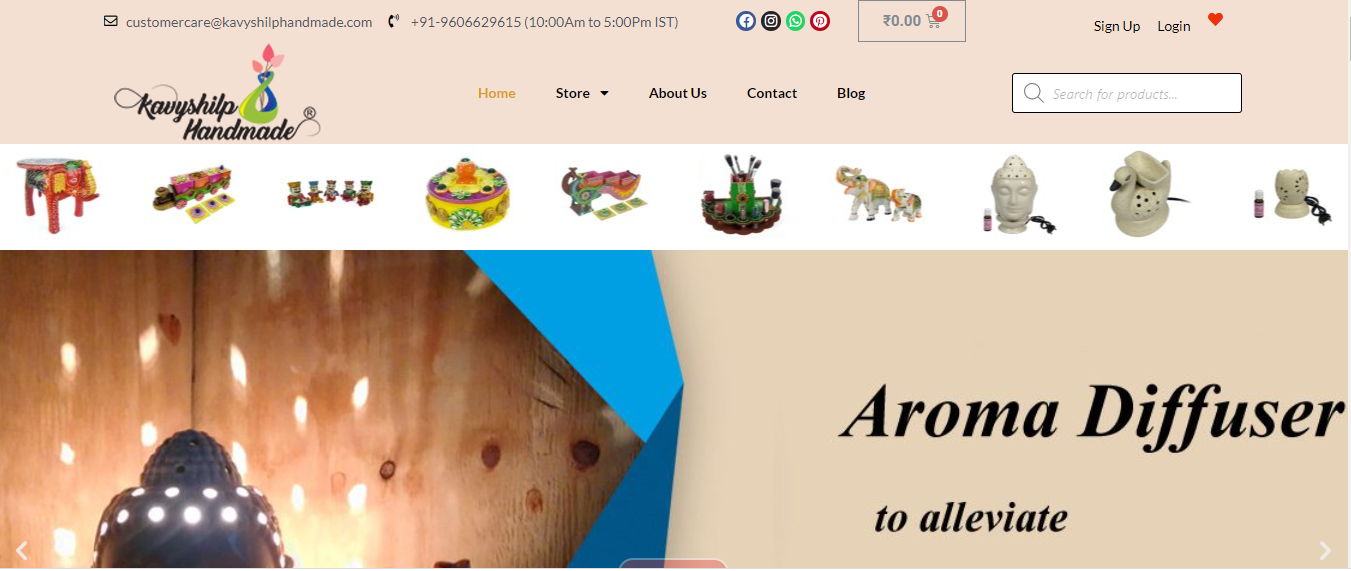
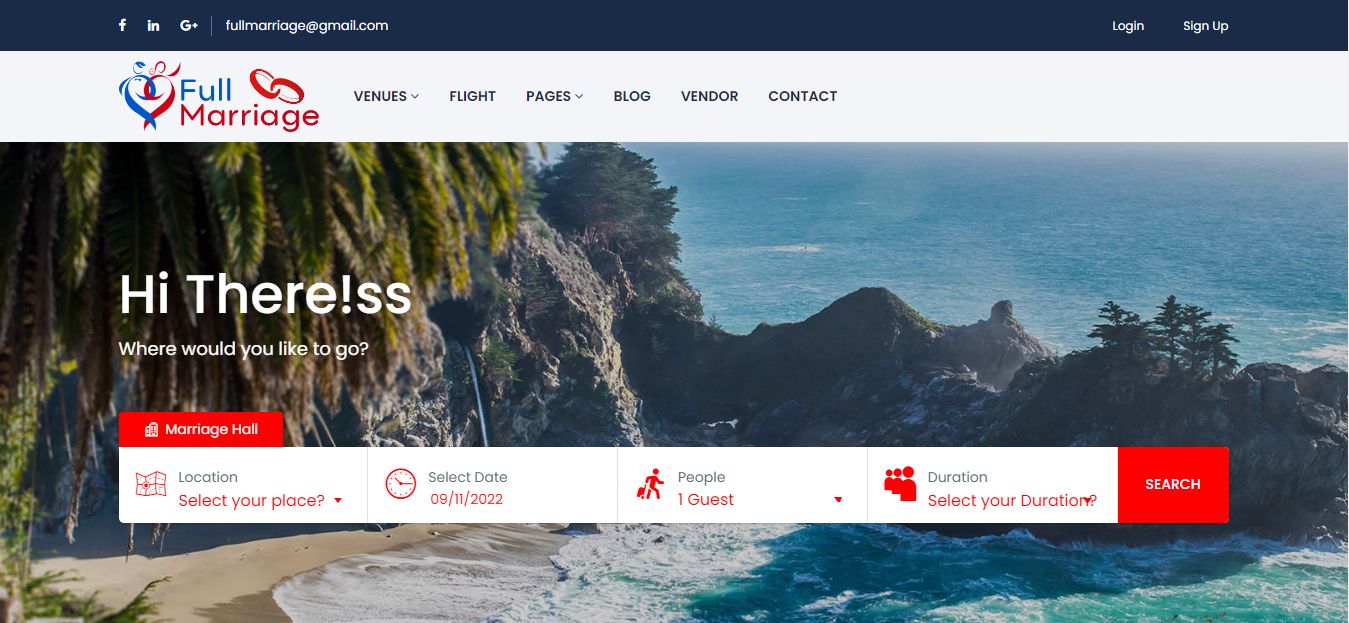
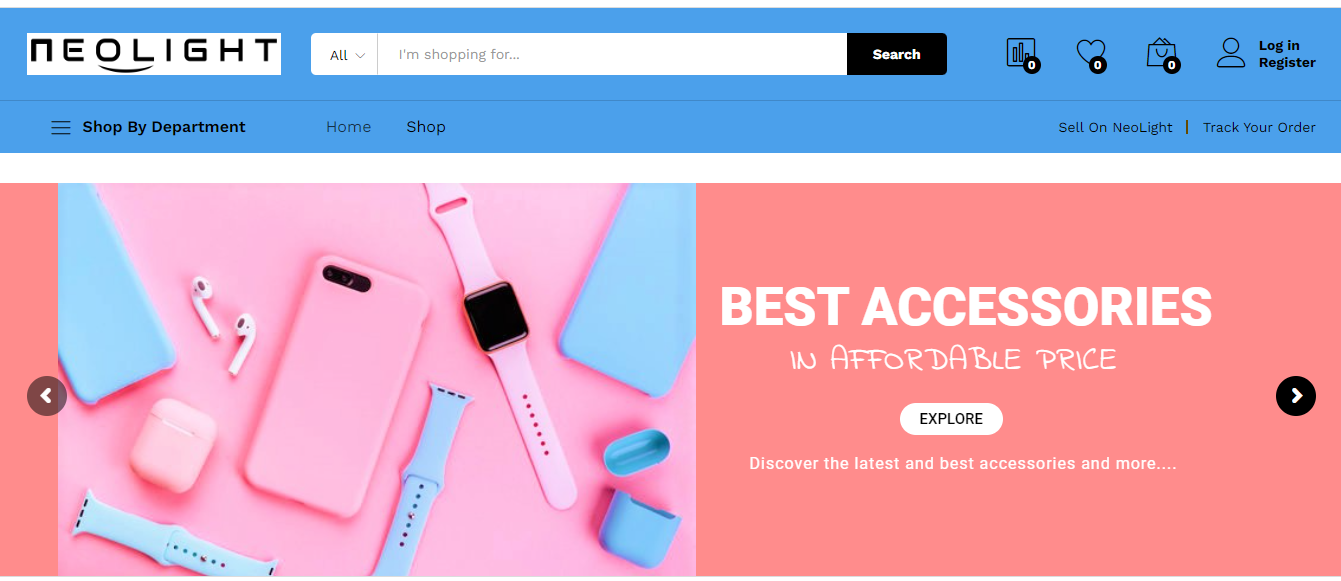
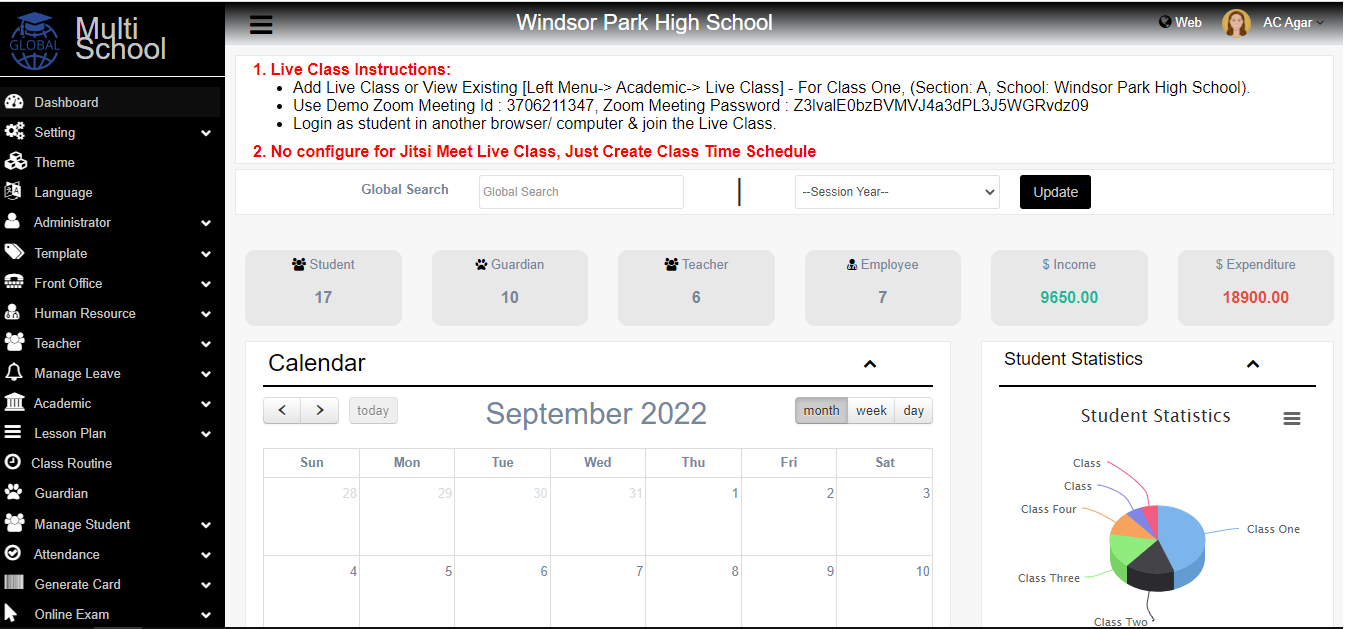
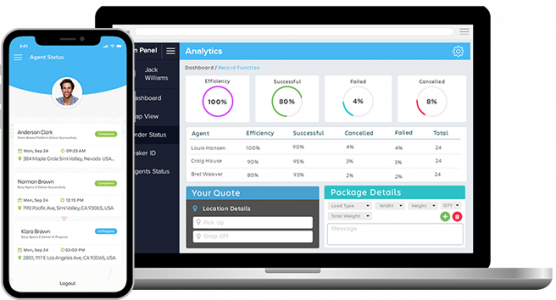
E-commerce Development
We build fully responsive and user-friendly websites to provide commendable online shopping website solutions.
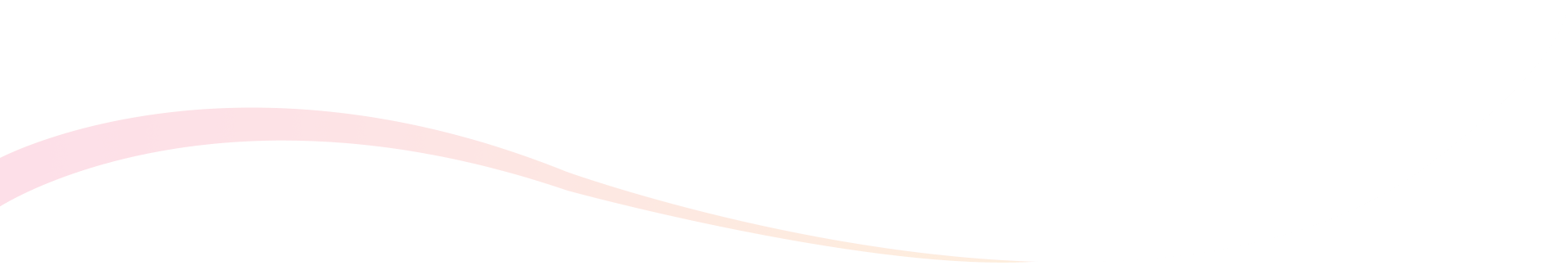
RPA Solutions
We help organizations build automated solutions focused on achieving cost reduction and reimagining processes to create intuitive systems.
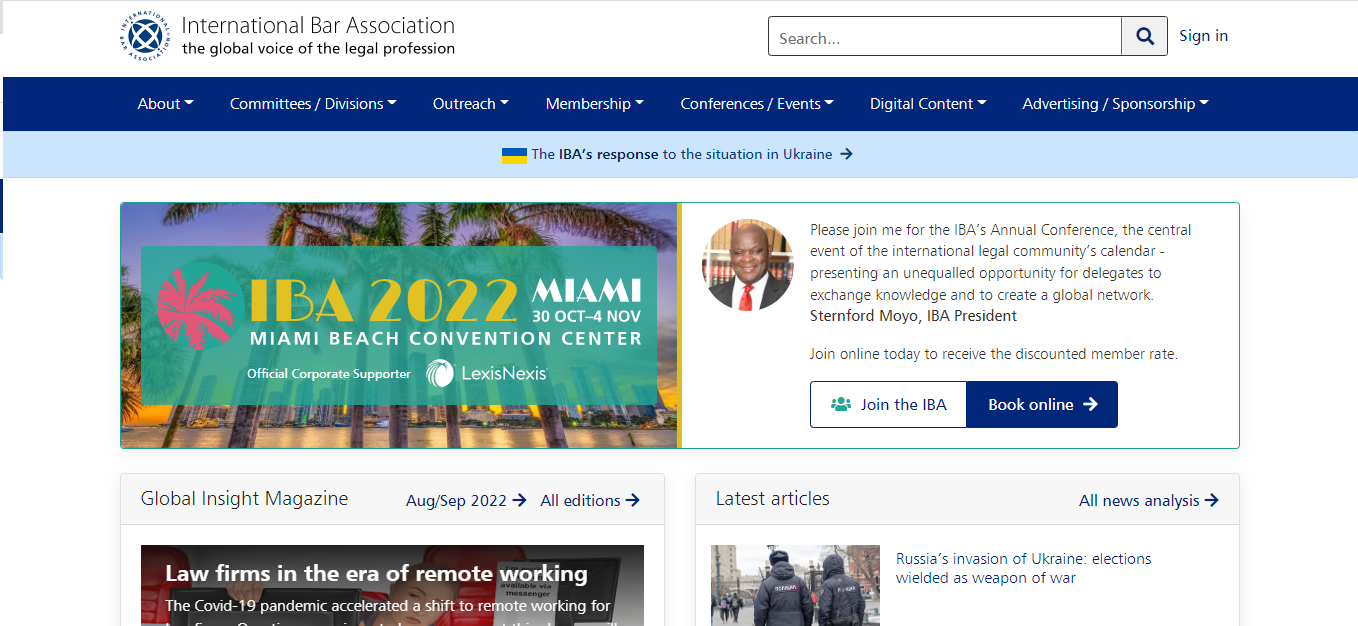
Web Development
The design of the website has to be catchy and at the same time, it should be simple
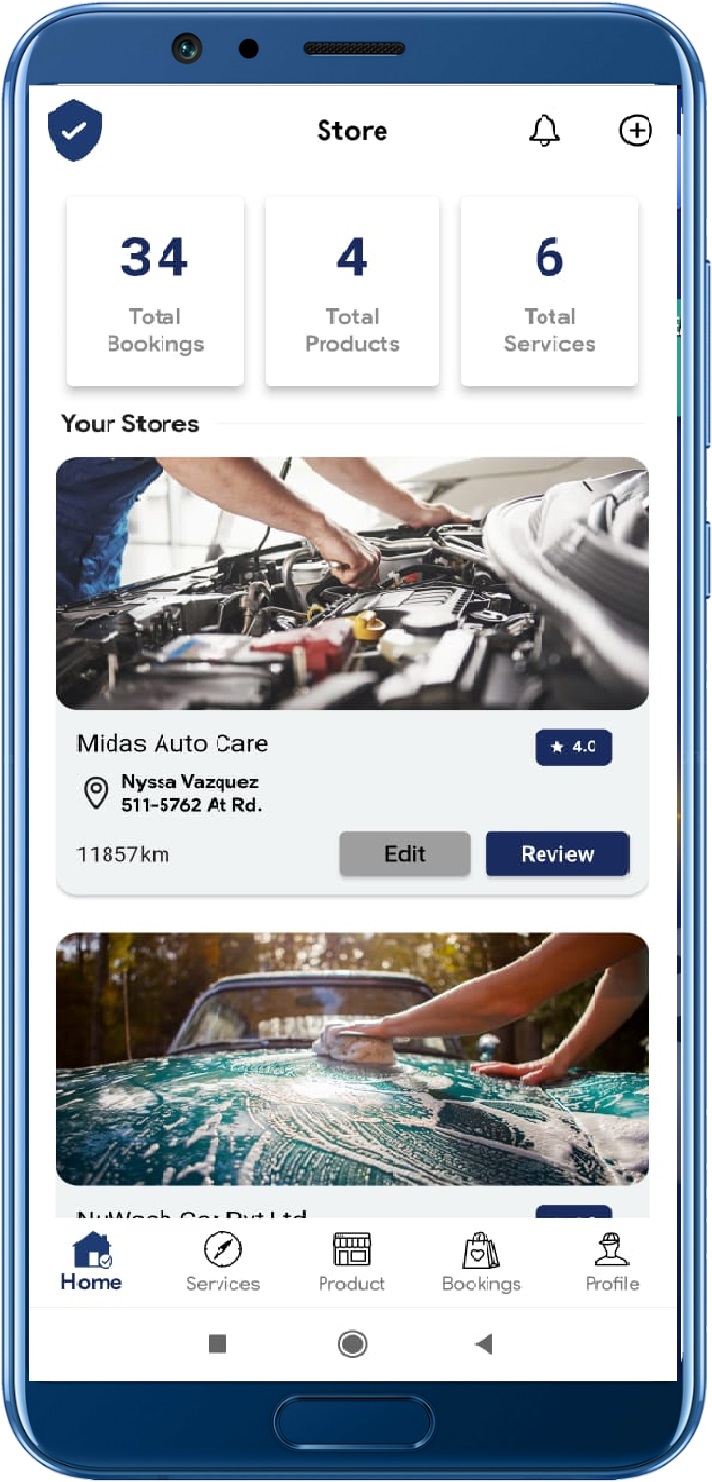
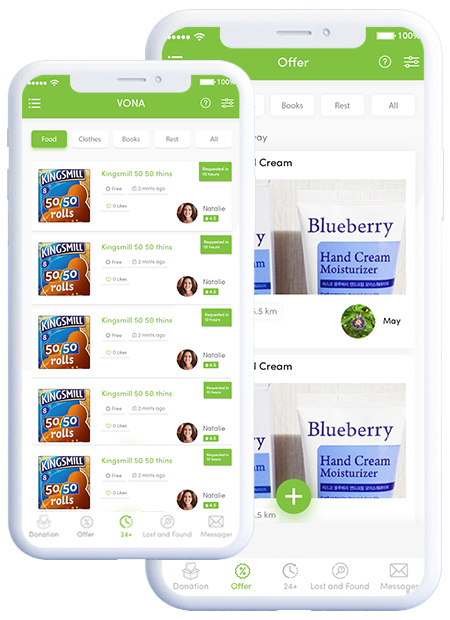
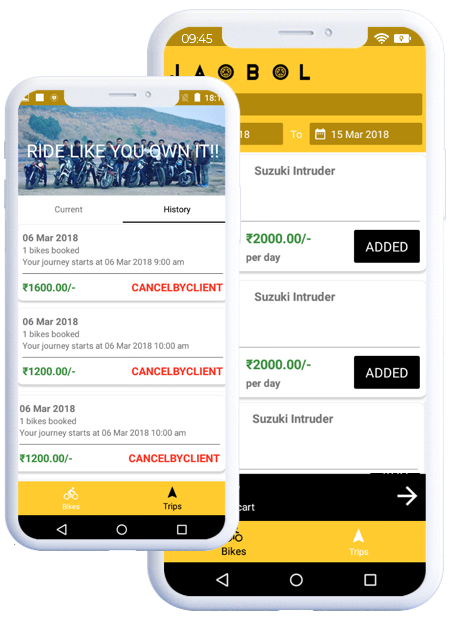
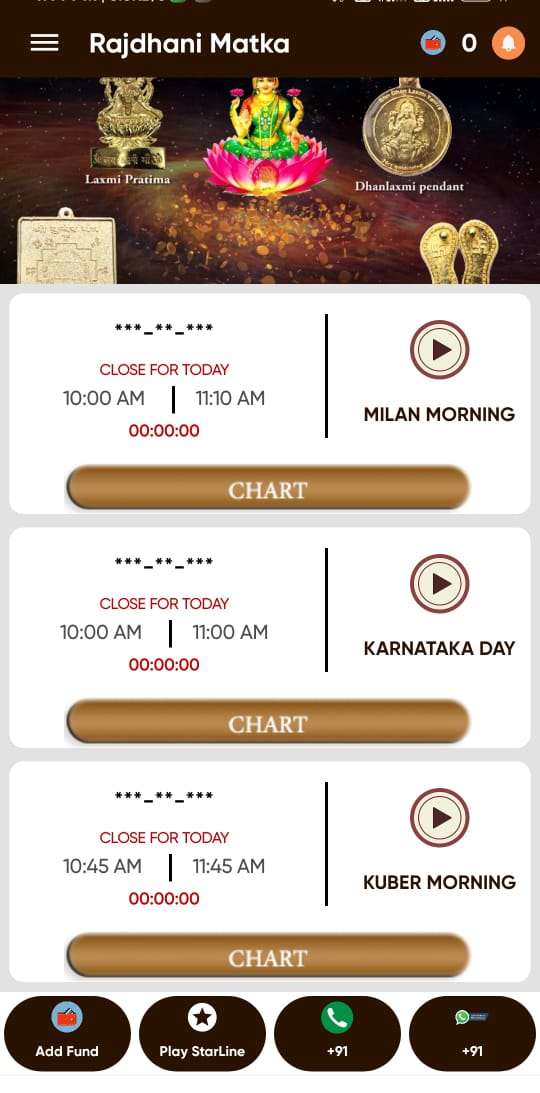
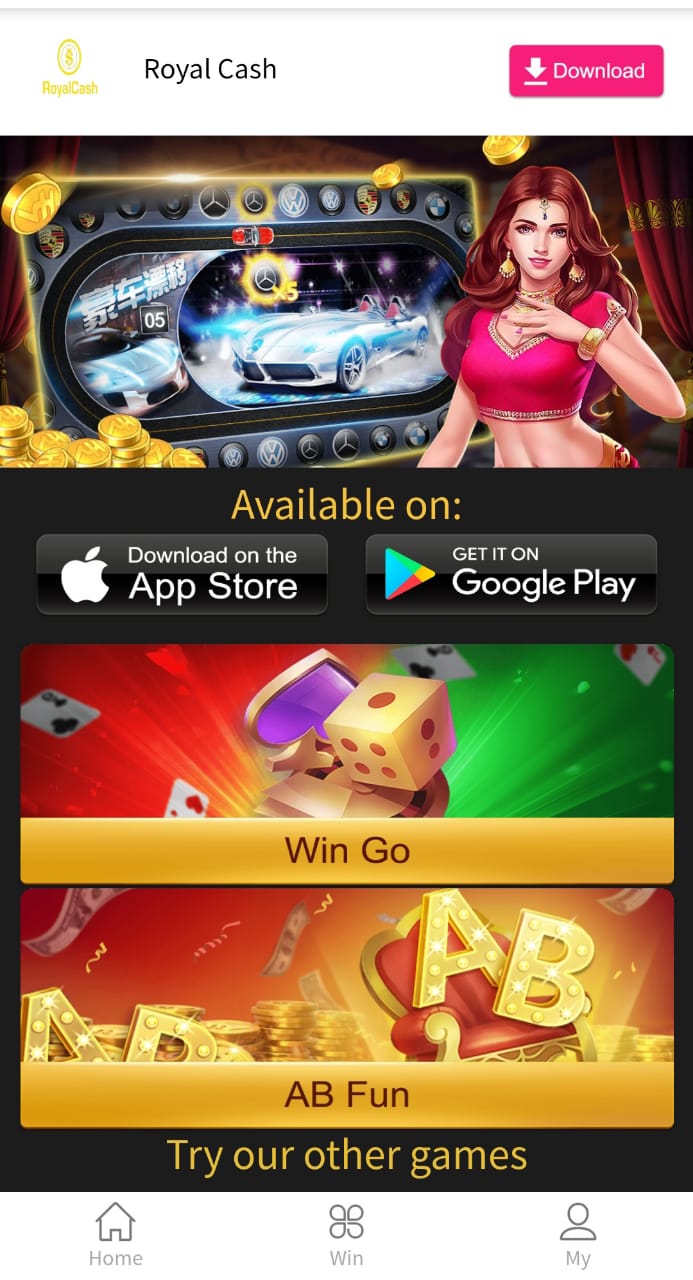
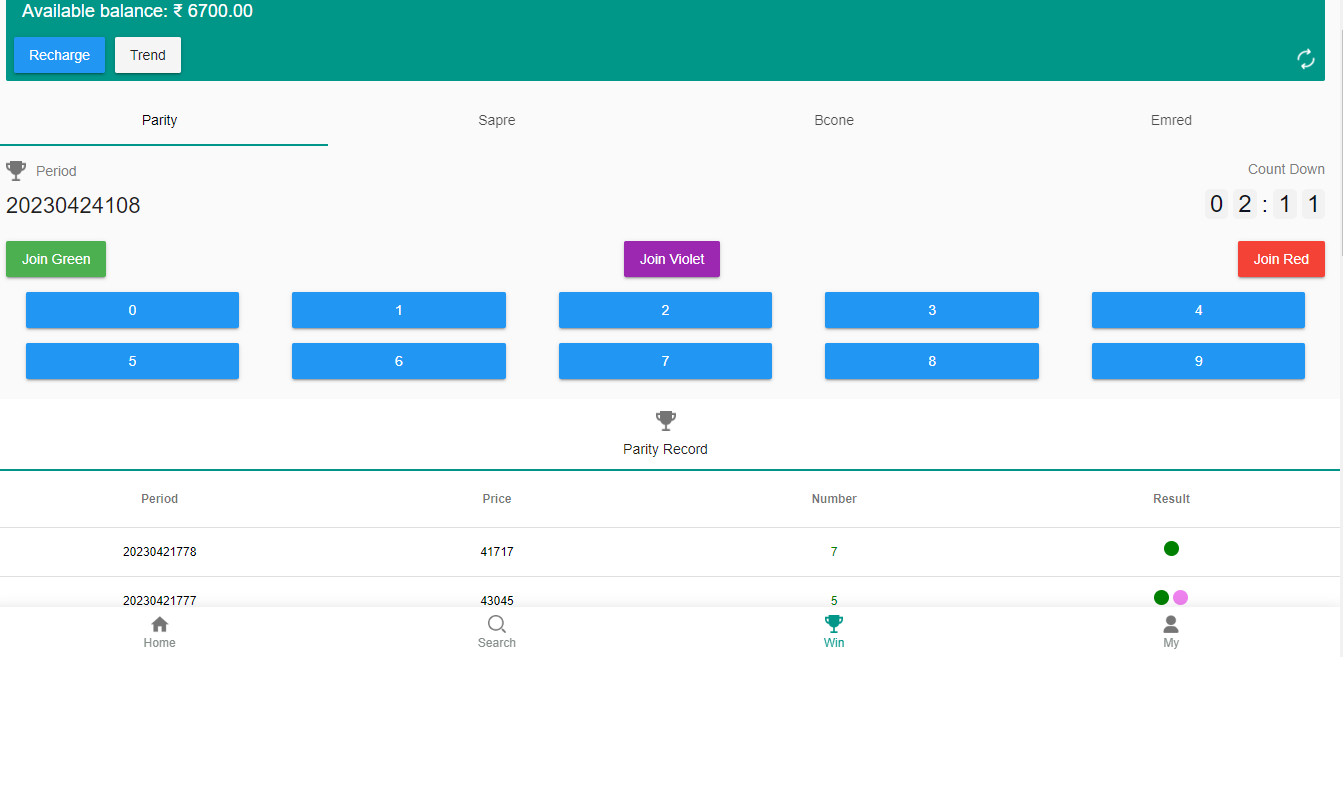
Mobile App Development
We provide mobile app development services to start-ups to enterprise-level companies..
Game App Development
Our certified gaming software development experts can create your video game project from scratch or revamp existing solutions with updates and integration.
Digital Marketing
In order to make your website recognizable, you need optimization of the website to Stand Out.
AI Development
Discover new principles for your company with our AI-infused applications for smarter and better business-specific solutions
Our best efforts
All in One Destination for Custom Software Development, Apps, Website, AI, IoT & Blockchain Development Company
Delivering 100 % customizable clone Read-made Clone Apps | Clone Scripts | White-label Apps

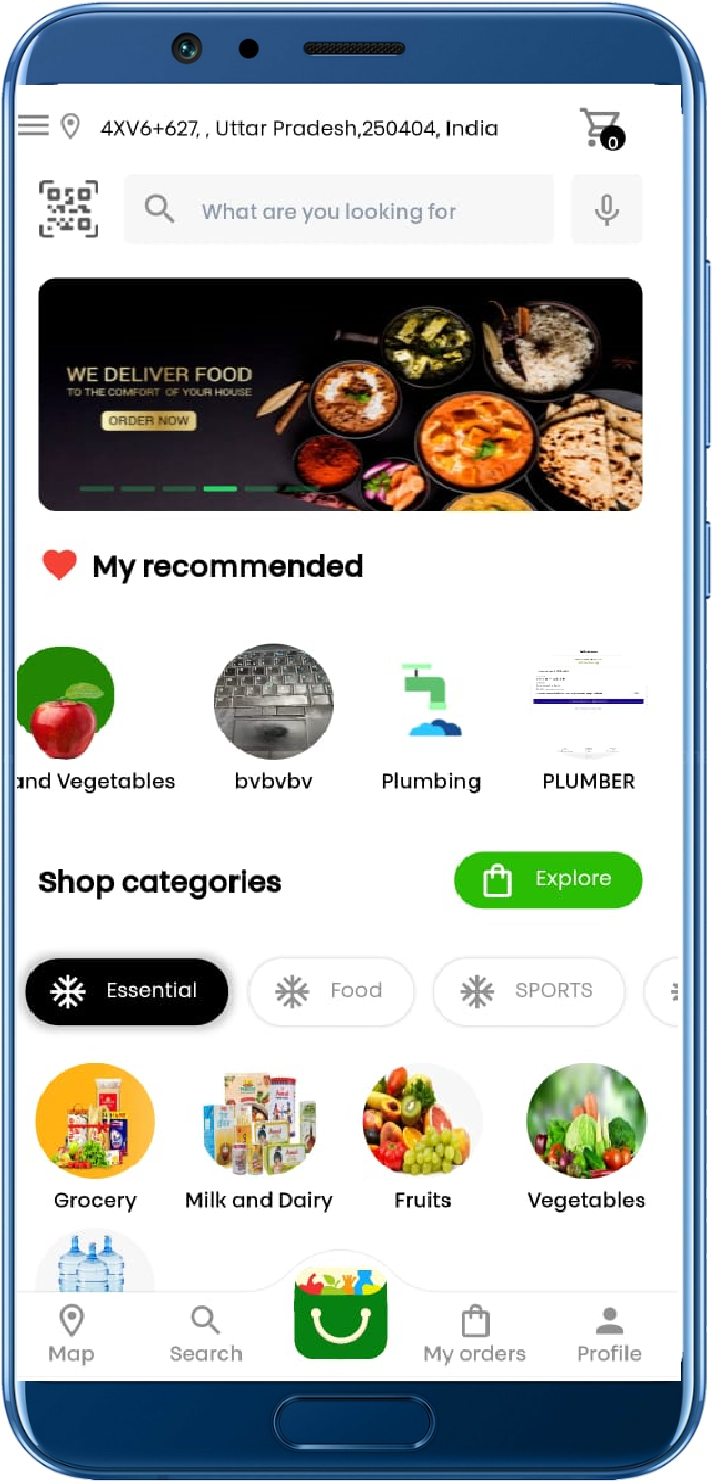
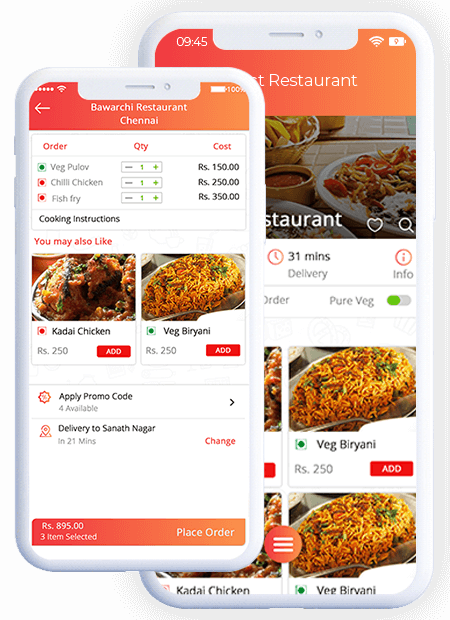
Food Delivery Solution
Ubereats Clone Improve Your Order, delivery and takeaway service business today! with our All in one delivery service solution
• App Installation• Advance Reports
• Responsive Web Panel's
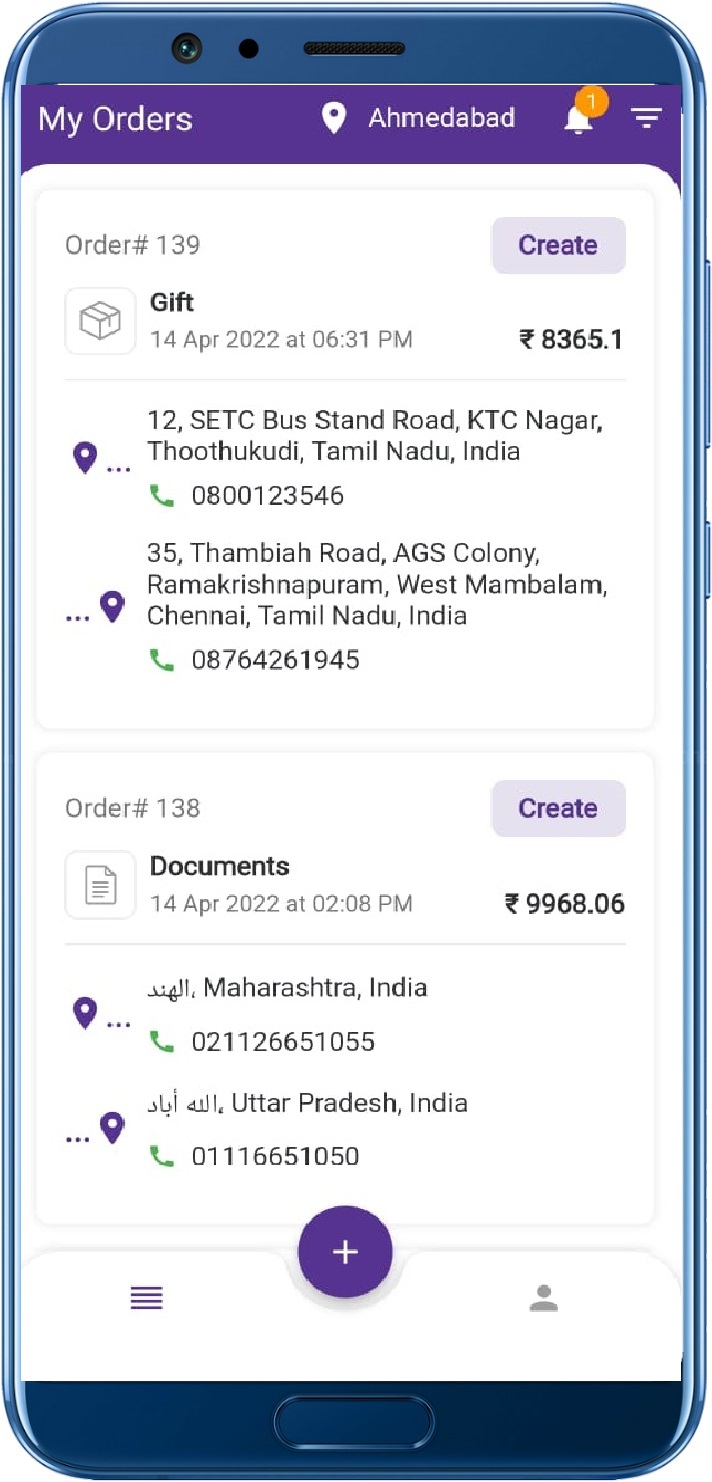
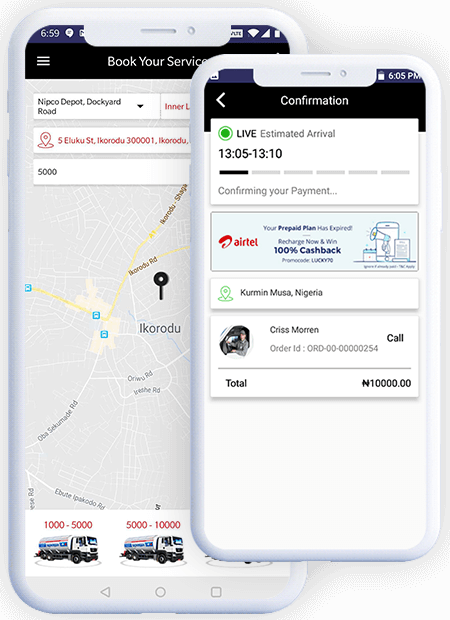
Uber For Trucks
Uber for Truck Manage your driver, fleet, partner and dispatcher operation accurately with our white label solution
• Life Time Licence• Licence Code Optimization
• Wallet

Uber For Taxi Booking
Uber Clone Manage your customer, driver, fleet, partner and dispatcher operation accurately with our white label solution
• White Labeling• Apps Approval on Playstore
• Advanced Analytics
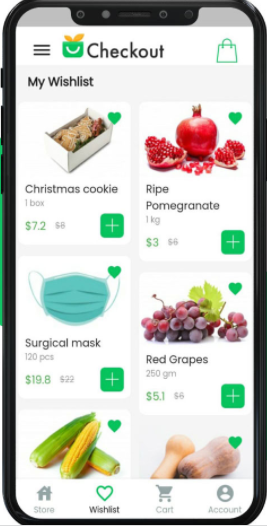
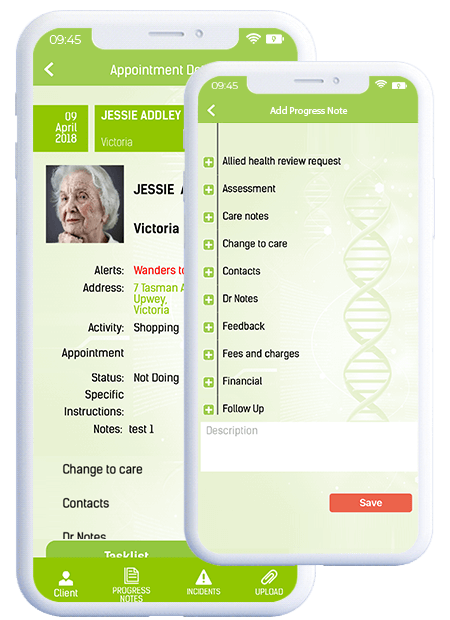
Create a Marketplace for B2B & B2C
We have the expertise to create your own marketplace for b2b & b2c manufacturers, Suppliers, buyers for any industry like Handyman services, Construction and many more.
• Launch your own branded online store• Fully Customize Your Business Solution
• Enhance Overall User Experience
• Streamline Your Business Operations
What We Promise
Our company values perfectly for all project & client
Custom App Development
We have expert professionals to develop your application from scratch
Satisfied Clients
We have expert professionals to develop your application from scratch
Dedicated Support
We provide excellent support during your initial stages to help your venture take flight smoothly. Satisfied worldwide customers
White-Label Solutions
Our clone scripts are white-label solutions that you can customize and create a unique application with our clone scripts
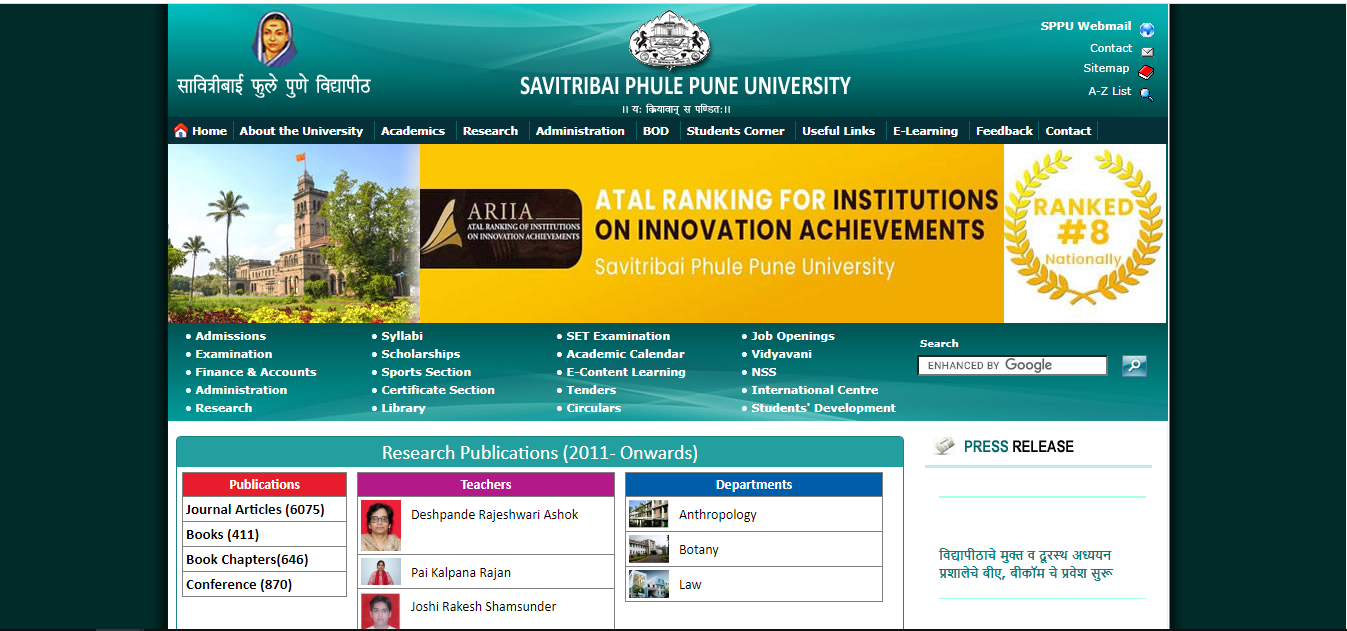
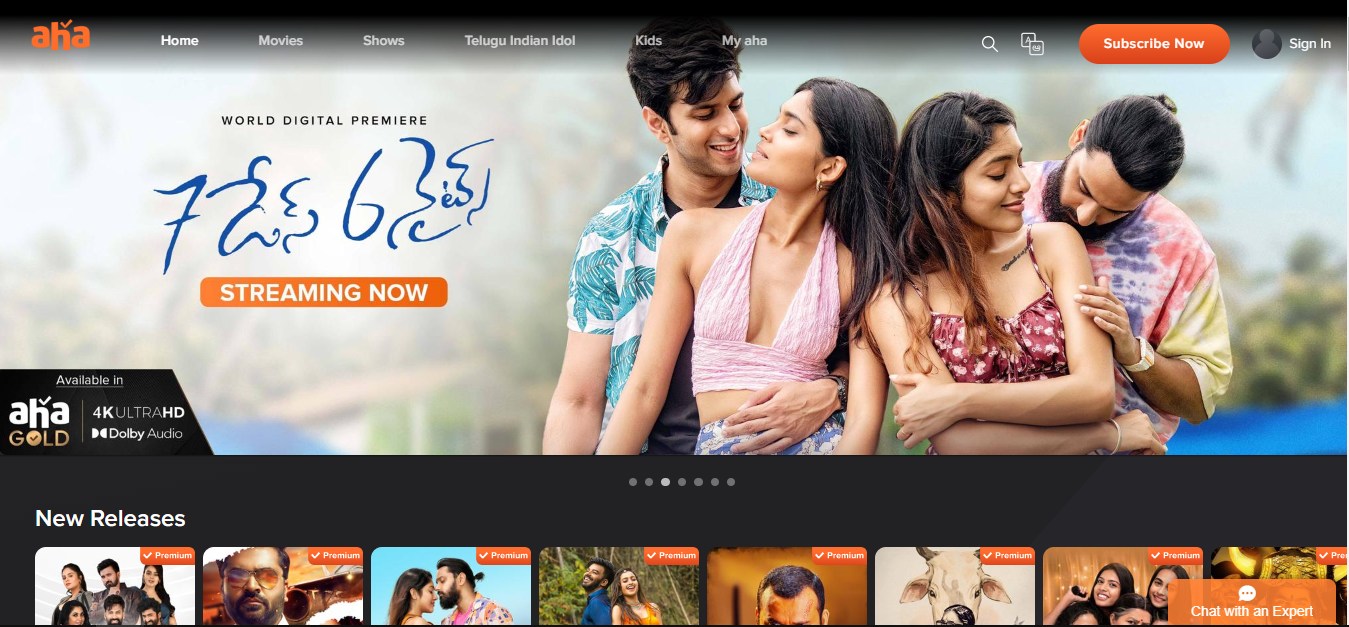
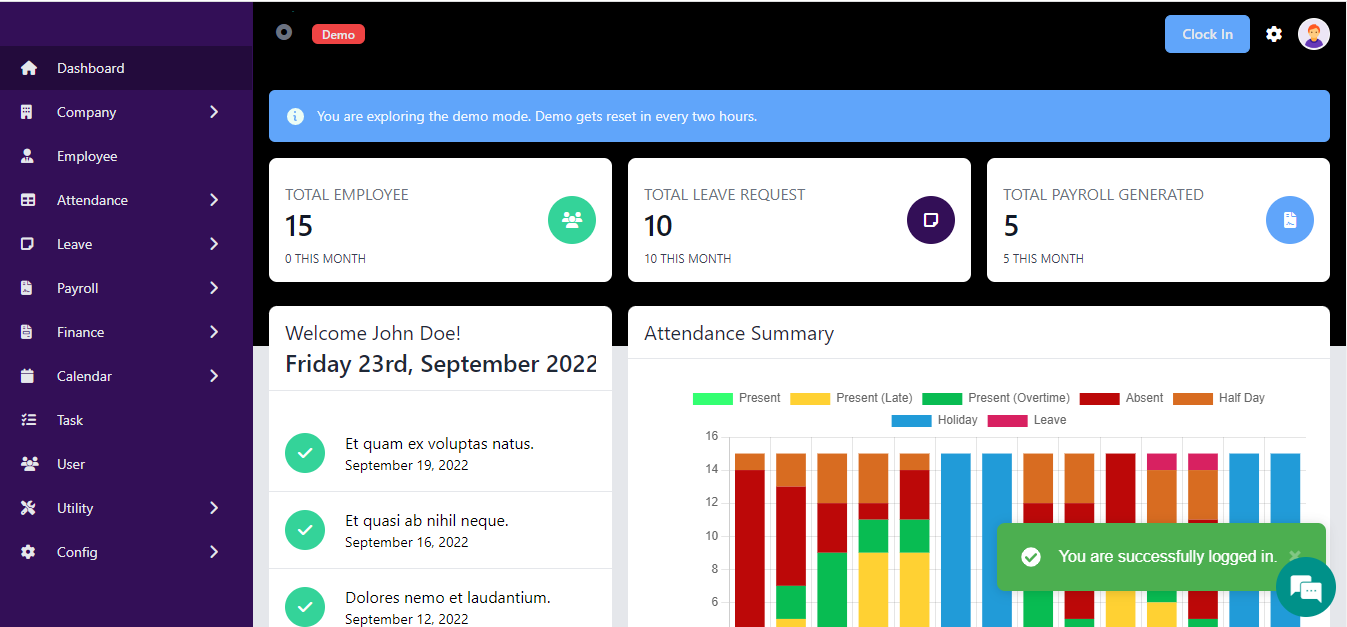
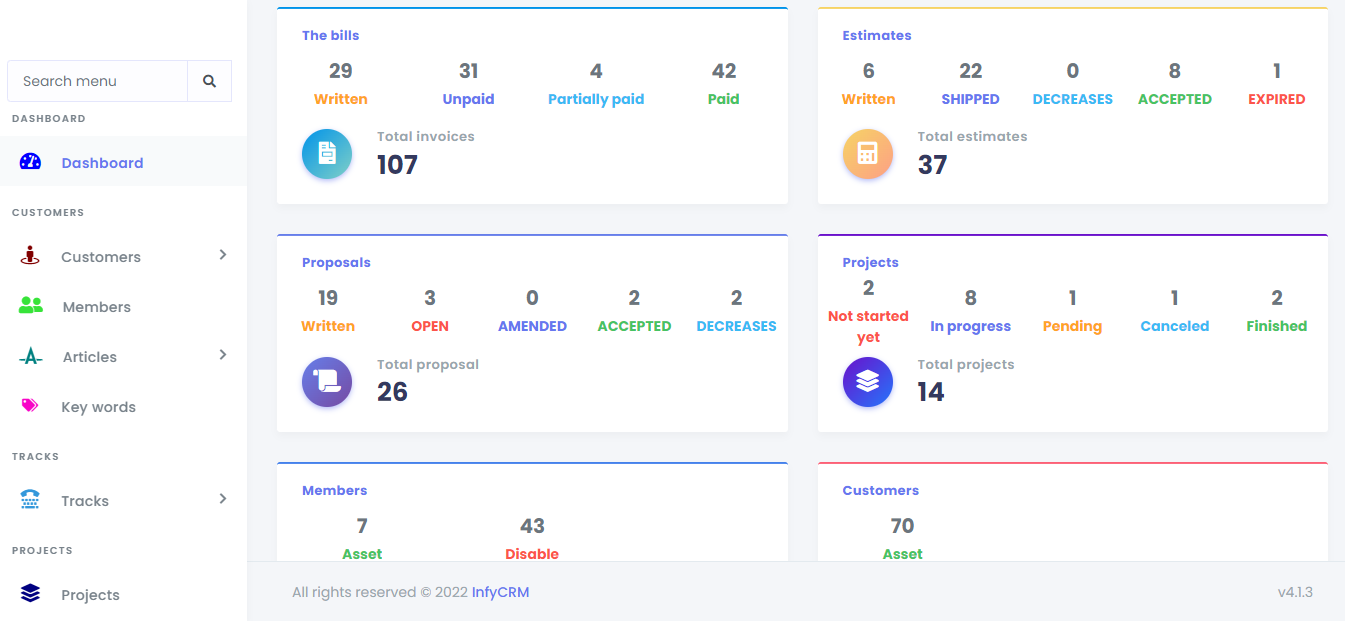
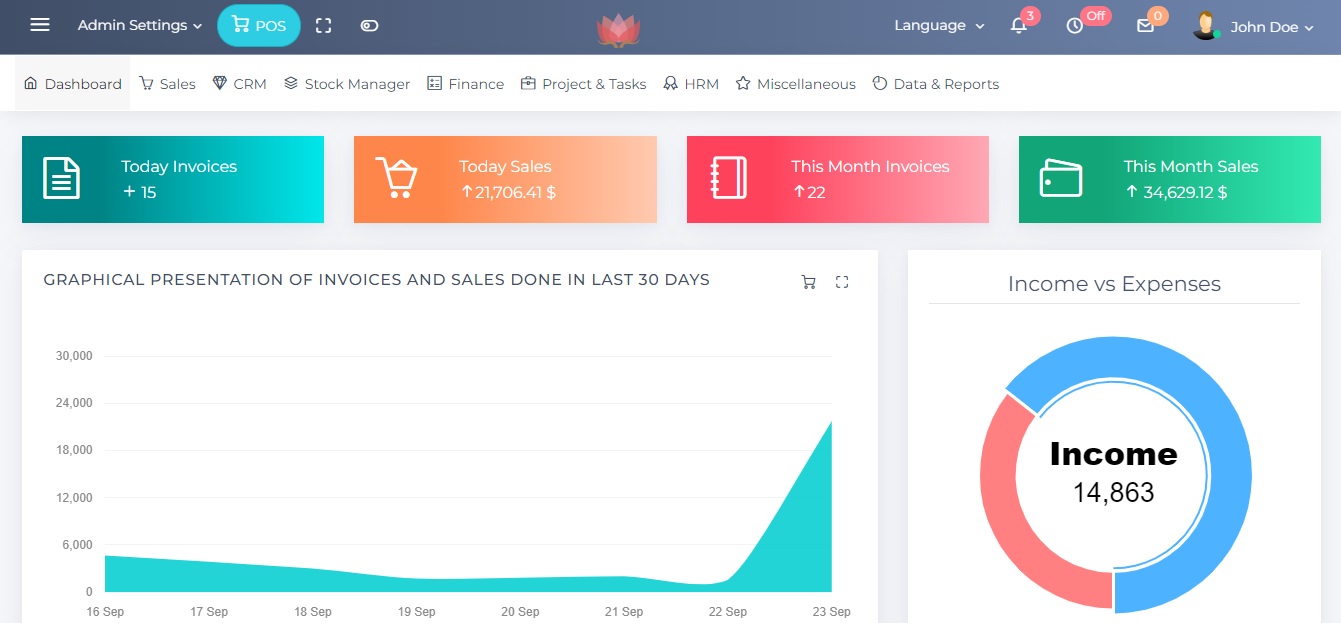
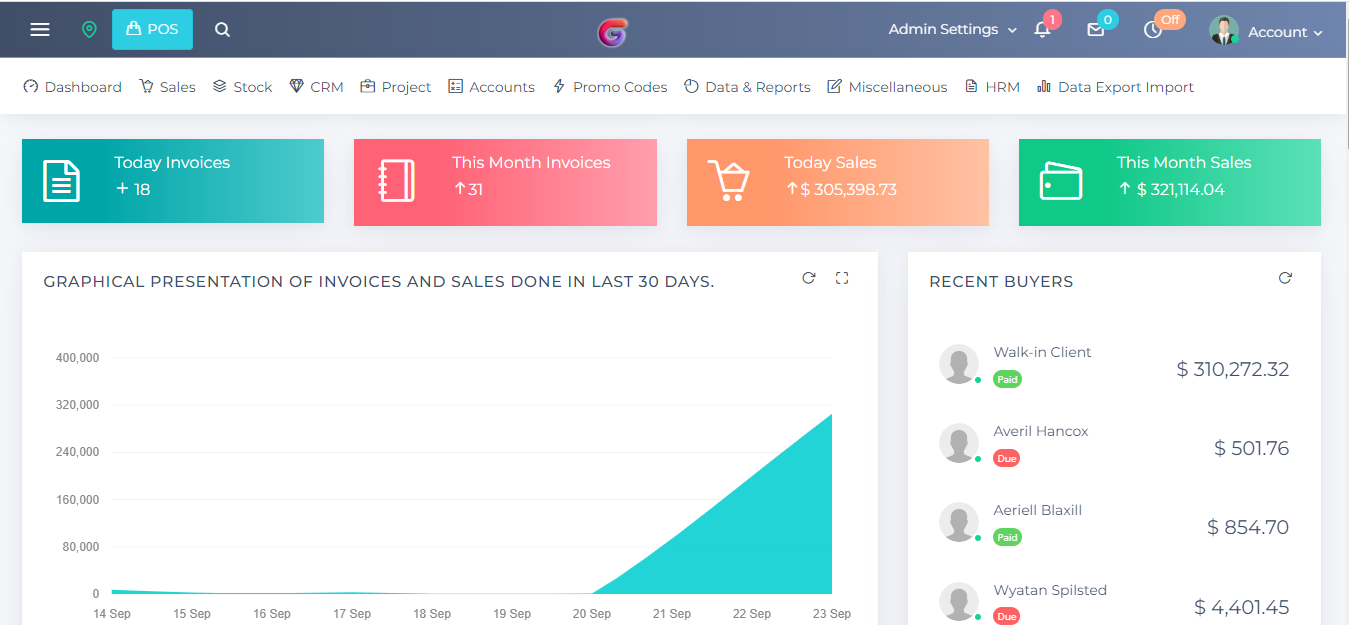
Portfolio
Take A Look At Our Latest Work
PRICING TABLE
Choose A Plan That’s Right For You
Silver Plan
6999
- 5 Pages Optimized
- 2 Mockups
- CSS Based
- SEO Friendly
- 1 Feedback/Inquiry Form
- Domain Registration
- 1 year Web Share hosting
- Free Email Account
Gold Plan
14999
- Responsive Website
- 10 Pages Website
- 3 Mockups
- CSS Based Website
- Social Media Marketing
- SEO Friendly
- Google Analytics
- 2 Feedback/Inquiry Form
- Domain Registration
- 1 Year Web Hosting
- Free Email Account
Diamond Plan
29999
- Responsive Website
- Up to 20 pages website
- 5 Mockups
- CSS Based
- Social Media Integration
- SEO Friendly
- Google Analytics Integration
- 3 Feedback/Inquiry Form
- Domain Registration
- 1 year Hosting Plan
- Email Accounts
- Control Admin Panel
TESTIMONIAL
See What Our Clients Say’s
Sneha
CEO and Founder
Thixpro did a great job developing our website. Whether providing direct development support or giving us the opportunity to make our development updates, Web Design expertise and support services were top notch! It didn't take long to stand up our website, and we were pleased with the design and layout of the graphics and information. We look forward to engaging with Toinette again, especially as we look to build out our site services.
Cak Dikin
CEO and Founder
Thixpro was referred to me by a trustworthy friend. After reviewing his website, I decided to give Thixpro a try. I am happy to say I was not disappointed! From the onset, I knew Thixpro was a team I could work with. I worked with Them, who listened to my desires and offered professional advice and expertise. Re-building our website came with challenges that Toinette did not back down from. She kept me informed every step of the way and met every deadline.
Smriti
CEO and Founder
Having my website created by Thixpro, I was able to increase my consumer base by 60 percent! The professionalism and individualism of the customer service I received from Thixpro is unparalleled. To see that this web design company was able to create my vision on the web was incredible as they did not leave out any details and collaborated with me through the process to assure that I was completely satisfied. I highly recommend it to everyone!
We work in different Industries
Industries
We Cater To Almost All Industries, With More Than 50+ Clients And 130+ Projects All Over The
World,
experts cater to the growing demands providing efficient solutions to the logistics & distribution
industry. We have extensive experience and relationships in serving their needs. We solve complex
sequences in Logistics operations simplifying the flow in each area. We help our clients in meeting
their dynamics in global markets with our prominent on-time solutions.
Our Blogs
Latest News & Blog

ERP
Workday vs. PeopleSoft which is Right for Your Business
Workday vs. PeopleSoft which is Right for Your Business
Hundreds of vendors are fighting for a piece of the HR software market. Of the companies aspiring to rule your vast and complex human resources technology, the most epic battle rages between Workday and PeopleSoft . Both are strong choices with a loyal
Read More
ORACLE
Oracle Rolls Out Soar to Soar its Cloud Business
Oracle Rolls Out Soar to Soar its Cloud Business
The company claimed that its new solution comes with automated tools and cloud transition methodologies that can allow customers to migrate to cloud in just 20 weeks. Oracle Soar also enables customers save time and reduce cost of cloud migration by up
Read More
DATA PRIVACY / GDPR / PEOPLESOFT
Myths of GDPR
Myths of GDPR
Only 2 weeks left before the enforcement of the General Data Protection Regulations (GDPR) and there is FEAR! And fuelled by it there is paranoia surrounding what needs to be done. Rumors. Assertions. And crazy ideas. In this blog: we will bust all the
Read More
ORACLE
Top 5 Benefits of the RPA
Top 5 Benefits of the RPA
RPA tools are known for their tactical, focused, and agile approach for accelerating the manual processes. RPA helps employees from mundane, repetitive tasks and leverages their human skills for more important tasks, where human-touch is necessary.
Read More
ERP
Leverage the Power of WORKDAY into Your BPM for Robot Business Operations
Leverage the Power of WORKDAY into Your BPM for Robot Business Operations
Even after streamlining the business processes and workflows with ERP and BPM products’ help, the need for the human effort has become inevitable, which is where the Robotic Process Automation (RPA) arrived.
Read More

APP DEVELOPEMENT
Best on-demand app startup ideas in 2022
Best on-demand app startup ideas in 2022
The world is full of inventions and we witness new and new inventions each day. People converted their problem-solving ideas to brilliant money-making ideas....
Read More
WEB DESIGN
Website Cost in India in 2022
Website Cost in India in 2022
Every business needs a website but creating a website within their budget is a real headache for new entrepreneurs. Before creating a website, a question arises in every non-techie person....
Read MoreOur Partners








Our Troop of Successful Clients










Copyright 2024 Thixpro. All rights reserved.